In case anyone wants to improve/change/use it:
CYBERSECURITY
-
WordPress categories covering AI topics
By
–
Web designers after reading this: https://t.co/yONuEtjT8L pic.twitter.com/p3y16ldruL
— Charly Wargnier (@DataChaz) 27 mai 2026Web designers after reading this:
-

Perplexity Open-Sources Bumblebee npm Security Scanner
By
–
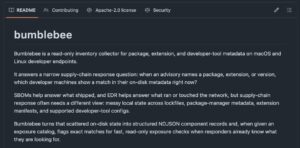

Perplexity open-sourced the scanner it uses to triage npm worm waves. Bumblebee reads on-disk metadata only, never runs the package manager during a compromise. Exact (ecosystem, name, version) matching. 2,900+ stars in 5 days. Apache-2.0.
-
Prompt: Pain Point Mining for AI/Niche Tools
By
–
Prompt 2: "The Pain Point Miner" "Based on the [NICHE] projects you just found, I need
you to do deep research on the complaints and unmet
needs people are expressing around these tools and
this space in general. Search Reddit threads, X posts, Product Hunt comment
sections, -

The Security Risks of Shadow AI in the Enterprise
By
–
The Shadow AI Crisis — download the report here: https://
josys.com/resources/shad
ow-ai-crisis
… Summary:
Shadow AI use is rampant, with 78% of professionals using AI tools in their daily workflows. Yet 70% of organizations lack visibility into these tools, creating significant data exposure risks. -
AI swarm attacks: Is your business ready?
By
–
AI Swarm Attacks Are Coming — Is Your Business Ready? AI-powered swarm attacks could become the next major cyber threat, using coordinated intelligent systems to overwhelm defences at unprecedented speed and scale. Read more https://
bernardmarr.com/ai-swarm-attac
ks-are-coming-is-your-business-ready/
… #AI #CyberSecurity -
OpenAI Launches Daybreak, an Agentic Cybersecurity Tool
By
–
OpenAI just launched a new cybersecurity product called 'Daybreak' that pairs GPT-5.5 with Codex to act as an agentic security team across a codebase.
— The Rundown AI (@TheRundownAI) 11 mai 2026
The product scans repositories, identifies vulnerabilities, generates patches, and automates detection and response.
It ships… pic.twitter.com/WdZkgIPZMoOpenAI has just unveiled a new cybersecurity product named 'Daybreak,' which combines GPT-5.5 with Codex to function as an autonomous security team for a codebase. The tool scans repositories, detects vulnerabilities, generates patches, and automates threat detection and response. It is now available.
-
Autonomous AI Agents: Hacking and Self-Replication
By
–
A few days ago, Palisade Research confirmed that AI agents can now autonomously hack remote computers and self-replicate, with success rates jumping from 6% to 81% in just one year. In tests, a Qwen 3.6 agent navigated across four countries, installing its own weights and launching operations.
-

Server Security Recommendations: Firewalling and SSH Access
By
–
Enter Lenny's Buildathon: https://
lennysbuildathon.replit.app
