next up: Claude Code with @bcherny and @_catwu ! a short history of claude code from cli to ide to desktop to sdk
SECURITY
-
Hetzner VPS Security: Tailscale, Cloudflare IPs, and SSH Lockdown
By
–
feature 3: dreaming same thing as shipped in claude code – demo shows it tying together nicely with outcomes to do automatic hill climbing
-
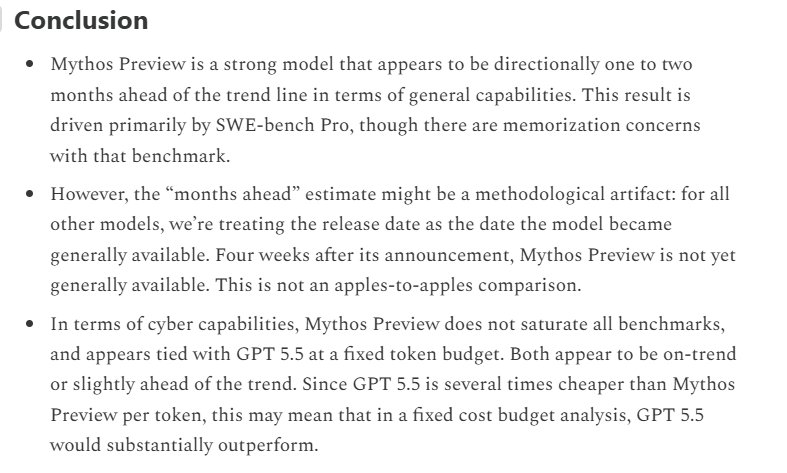
Claude Mythos and GPT-5.5 Cyber Capabilities Compared in Substack Article
By
–
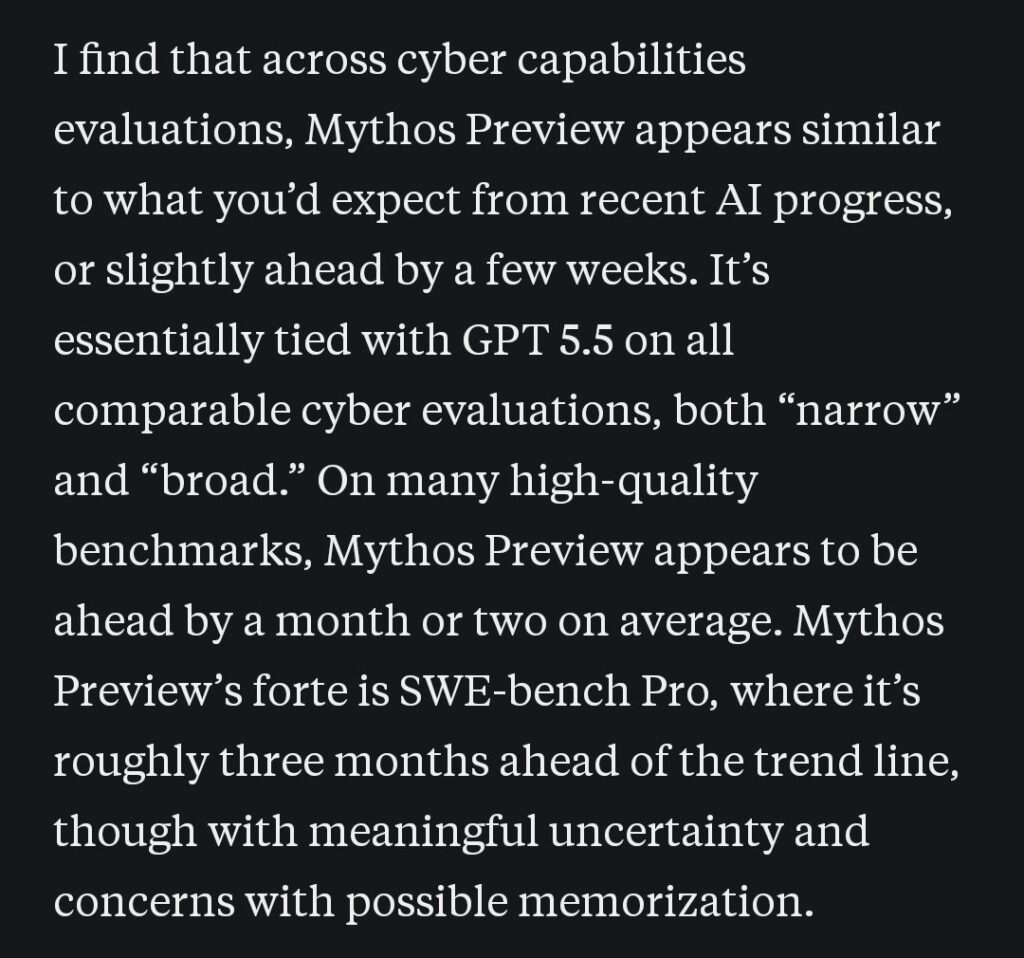
A very worthwhile substack (written by @natalia__coelho ) article that focuses particularly on Claude Mythos and GPT-5.5 cyber. tl;dr according to the analysis, GPT-5.5 is basically tied with Claude Mythos Preview on cyber capabilities, and may even be more cost-efficient;
-
NY AI Agents Event: Security and Openclaw at MCP Dev Summit
By
–
· Educational outreach through lectures, essays, blog posts (such as
http://
xgblog.ai ), social media ( @tabul_ai ), and other public work 6/9 -
Coinbase’s ‘Vibe Coding’ Financial Infrastructure: A Comparison to Traditional Banks
By
–
Most sites don't use libraries, they use external services to resize, for ex I used Cloudflare Image Resizing
-
Encrypt AI models end-to-end for true security
By
–
I just came across this Yale report on trust in Higher Education. The report confirms what many of us have known for a while: the trust in higher ed is low and only getting lower. Public confidence in higher education fell from 57% a decade ago to 36% in 2024, and even after a
-
AI Hackathon for Document Analysis, Risk Flagging, and Data Protection in India
By
–
Same point why they're so easily replaced with AI There's no business anymore for all these SaaS in future when everyone finds out and asks their AI!
-

SSH Key Limitations Against SSH 0-Day Vulnerabilities
By
–
.
@Redisinc is returning to Interrupt! Say hello to their team at the expo hall to learn about their fast memory layer for chatbots and AI agents as well as their ready-to-use tools for building AI apps. -
Flat Network Segmented with One-Way IT/OT Gateways
By
–
The company was running a flat, unsegmented network before implementing one-way gateways between IT and OT systems.
-
Hardware Data Diode Blocks Inbound Traffic to OT Production Systems
By
–
Hardware-enforced one-way data transfer blocks all inbound traffic to production systems. Data flows out for monitoring. Nothing flows back toward OT. A Vietnamese chemical company eliminated communication vulnerabilities this way. Partner content with @OPSWAT. #opswat_ics pic.twitter.com/Z6Ovn1ddX1
— Lucian Fogoros (@fogoros) 5 mai 2026Hardware-enforced one-way data transfer blocks all inbound traffic to production systems. Data flows out for monitoring. Nothing flows back toward OT. A Vietnamese chemical company eliminated communication vulnerabilities this way. Partner content with @OPSWAT
. #opswat_ics